Built for a
sovereign internet
QANAT's WEB X. OS is a full-stack sovereignty ecosystem from identity and encryption to data licensing and network governance. Every layer is designed around one principle: you own it.

A full-stack sovereign
operating system.
Apps and services built by developers and enterprises run here. The top-most user-facing layer, an open ecosystem governed by smart contracts.
All sovereign applications run natively inside WEB X. OS. They install as .wxa packages at runtime without modifying the OS codebase.
Blockchains are plugged in as the transaction layer. Any chain can be added modularly. The OS is chain-agnostic and routes value without lock-in.
Seven integrated layers handle identity, data licensing, encryption, network routing, compute sharing, storage, and access control. Each layer is sovereign, composable, and replaceable. (detailed stack overview below)
Running on top of your operating system.
The foundation sitting directly on device hardware. Provides isolated execution environments, shared compute, and sovereign storage primitives.
Built Where It Matters
The blockchain is deliberately minimal. It processes QNT Token1 transactions and is modularly extensible by further chains. Everything else, including performance, intelligence and real-time coordination, runs on QNet, the system we engineered from the ground up for exactly this purpose.
Performance and Flexibilität
Safe Transaction
Performance and Flexibilität
Safe Transaction
1The QNT Token is used purely as an internal token for in-app and in-service operations within the QANAT ecosystem. It is not designed or distributed as an investment, security, or external currency.
A high-performance, scalable architecture
Engineered on best-practice design principles (SOLID, KISS, DRY) for efficiency, scalability, and maintainability. The only sovereign infrastructure that closes every gap, at every layer, simultaneously.
Authentication
Identity verification through secure trust checks, ensuring both parties are who they claim to be.
Encryption
Data protected with digital locks (e.g. RSA, ECC, Curve25519). Only authorised parties have the keys to access it.
Data Licensing
Fair use and payment. You decide what's shared, under what conditions, and can even earn from it.
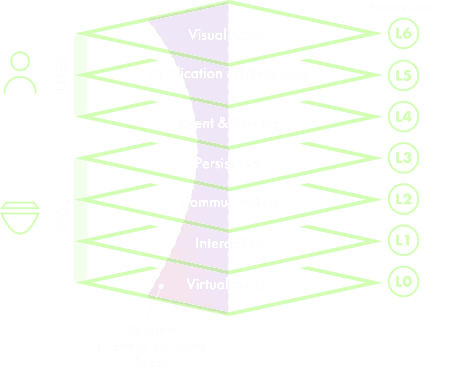
Presents data and functionality in a human-readable format through UIs and UX design, using technologies such as Flask, HTML, JavaScript, and CSS.
Orchestrates services and microservices within the QANAT.app ecosystem to execute complex business processes, including service coordination, transaction management, and error recovery.
Manages events, system notifications, and asynchronous event chains across multiple nodes. Also abstracts complex services like microservices, smart contracting, and token-fiat exchange into reusable components.
Stores and manages data in a structured format, abstracting the underlying data handling so developers can work with high-level constructs. Controls QANAT's data governance and integrity.
Responsible for sending and receiving data (messages, video, etc.) via TCP/IP and UDP, while managing packet routing, optimal data paths, and logical addressing.
Handles all user-to-node and node-to-node interactions, as well as system processes like device configuration, fitness rate calculation, and user login.
Ensures compatibility across operating systems and manages the decentralised overlay network topology, including its structure, optimisation, and configuration.
No blind spots. Zero gaps. QANAT addresses every data touchpoint across the stack: from hardware and OS, through the sovereign platform layer, to the application and marketplace tier.
Full-Stack Security Framework
Six interlocking primitives that turn sovereignty from a principle into a working system — from cryptographic identity at the edge to a peer-to-peer network layer that cannot be selectively shut down.
Self-Sovereign Identity (SSI)
Your identity is built on decentralised identifiers (DIDs) and verifiable credentials. It exists independently of any platform lives in your wallet, and is cryptographically yours alone. No central registry can revoke it.
End-to-End Encryption
All data transmitted within the QANAT network is encrypted end-to-end. From messages to file sharing and app data only the intended recipients can read what you send. Perfect Forward Secrecy by default.
Zero-Knowledge Proofs
QANAT uses ZK proofs to let you prove facts about yourself age, membership, credentials without revealing the underlying data. Verify without disclosing. Authenticate without exposing.
Data Licensing Protocol
Define exactly who accesses your data, for how long, and at what price. Smart contracts enforce the agreement automatically consent is programmable, enforceable, and revocable.
Decentralised Storage
Your data is distributed across a sovereign storage network where you hold the encryption keys. IPFS-compatible, content-addressed, and fault-tolerant. Your data exists even if QANAT doesn't.
QNet The Sovereign Network Layer
The peer-to-peer communication and routing layer that binds the QANAT ecosystem together. Built for resilience and censorship-resistance QNet cannot be selectively shut down.
From idea to shipped
in 7 steps.
Define the app’s ID, name, version, category, and required permissions. This file is the app’s passport, verified on every install.
Create a React / TypeScript component (.tsx) that renders inside the OS shell with full access to the design system and system APIs.
Add your own endpoints to the Flask backend. The OS namespaces and routes them automatically after installation.
Add the component mapping to app-registry.tsx so the OS knows which React component to load for your app ID.
Wire the install button to the backend endpoint. Upload, extract, register, live. Asset serving and desktop placement are handled automatically.
Close windows, delete the backend directory, deregister from the frontend. Clean, complete, and reversible at any time.
One CLI command bundles everything into a verified, checksum-signed .wxa file. Submit to the WEB X. OS App Store.
Runtime Apps
Apps are self-contained .wxa packages: ZIP archives with a manifest, UI component, and assets. They install and uninstall at runtime with zero changes to the OS codebase.
Two Build Modes
Choose Builtin for full React and TypeScript components with native OS theming, or iframe to wrap any existing web app and deploy it as-is.
Permissions & Distribution
Apps declare exactly what they need: network, storage, identity. Users see it clearly at install time. Signed packages ship directly to the WEB X. OS Marketplace.
Our Design Principle
QANAT flips the pyramid by putting privacy and true ownership first without sacrificing user convenience.
From insecure Web
to private & full control end-to-end Ecosystem
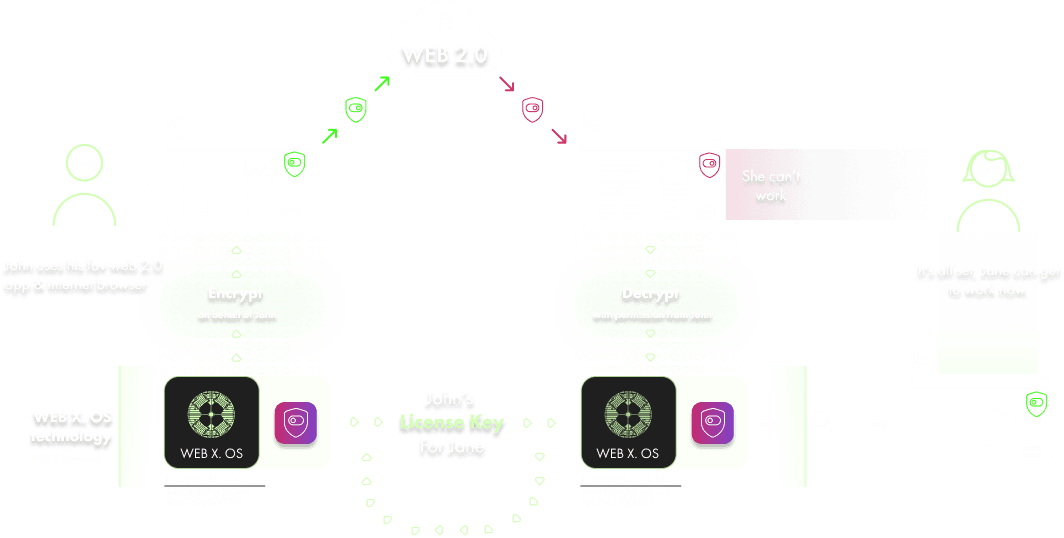
John's data is automatically encrypted to ensure seamless acceptance by the provider platform, without any restrictions. John is the only person who can decrypt this data.
John's data is kept safe using cryptography, which works in conjunction with the database technology and server-communication infrastructure of the WEB 2.0 provider services.
CIPHERX is responsible for the continuous management of John's data access and licensing. Only users who have been granted permission are able to access and edit John's data.
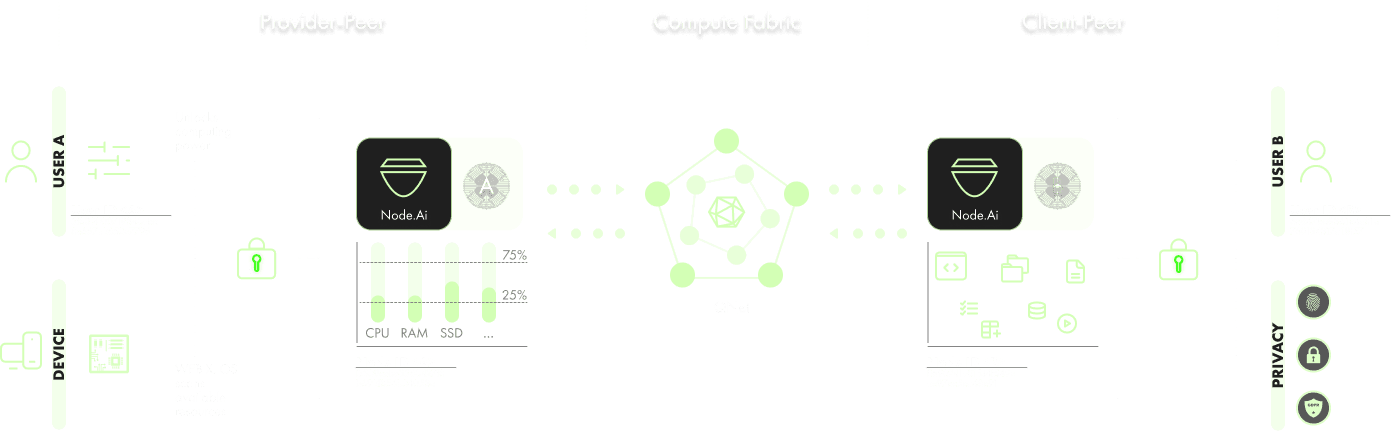
The WEB X. OS IoT stack shares unused hardware resources with the ecosystem. Node.Ai allows devices to monetize idle CPU, GPU, storage, or bandwidth in a secure, isolated execution environment. This ensures control, policy enforcement, and verifiable workloads.
CF is a decentr. compute marketplace where nodes contribute resources and execute policy-defined jobs under peer-to-peer contracts, monetized via the QNT token. Nodes are selected by reliability rating & HW fitness to ensure optimal, verifiable compute-to-data execution, without transferring data custody.
The client accesses decentralized compute with full privacy and data sovereignty. All data remains encrypted under the client's private keys, while Node.AI enforces policy and security at the network edge. Providers execute workloads without ever accessing the underlying data.